Cybersecurity is like the guardian of the digital realm. It’s all about protecting computers, networks, and the information they store from bad actors. Think of it as the lock and key for the internet. Just like you lock your front door to keep your home safe, cybersecurity is the digital lock and key that keeps your online world secure. It’s a must-have in today’s tech-driven world where everything from your personal photos to sensitive business data is at risk from hackers and cyber threats. So, whether you’re browsing the web, sending emails, or running a business online, cybersecurity is your digital shield, and it’s essential to stay safe in the virtual wild west.
When cyber security started
The 1970s marked the birth of cybersecurity, a crucial milestone in its evolution. The Advanced Research Projects Agency Network (ARPANET) played a pivotal role in laying the groundwork. ARPANET was essentially the precursor to the modern internet, a network designed for communication and information exchange. During this era, an event of note occurred. Bob Thomas, one of the developers involved with ARPANET, created a program that printed the message, “I’m the creeper; catch me if you can!” This program, executed on PCs connected to ARPANET, exhibited a novel behavior at the time. It autonomously moved from one machine to another. While this experiment was harmless, it is often considered the earliest recorded instance of a computer worm in the history of cybersecurity. This episode hinted at the challenges and opportunities that would come to define the field of cybersecurity in the years to come.
Types of Cybersecurity

1. Network Security:
Network security encompasses both software and hardware solutions aimed at preventing unauthorized access and service disruptions. This involves monitoring and responding to risks affecting network software (like operating systems and protocols) and hardware (including servers, clients, hubs, switches, bridges, peers, and connecting devices). It’s important to note that the majority of cyberattacks originate from network- based vulnerabilities. Network cybersecurity is specifically designed to oversee, identify, and address threats that target the network infrastructure.
2. Information Security:
Data security is a facet of information security that amalgamates various cybersecurity measures to ensure the preservation of the confidentiality, integrity, and accessibility of digital assets. This safeguarding of data applies both when the information is at rest (i.e., stored) and in motion (i.e., during transmission).
3. Application Security:
Application security is vital for thwarting unauthorized access and unauthorized use of applications and their associated data. Given that a significant number of vulnerabilities are introduced during the development and publishing stages, application security encompasses various cybersecurity solutions to detect weaknesses during the design and development phases. This proactive approach aims to identify potential exploits and notify teams for prompt resolution. However, it’s worth noting that despite best efforts, some flaws may still go unnoticed. Application security plays a crucial role in safeguarding against these vulnerabilities. One specific area within application security is web application security, which concentrates on fortifying web applications. These are often prime targets for cyber attacks. confidentiality of the supply chain and the organization it serves.
4. Cloud Security
Cloud security is primarily concerned with safeguarding assets and services hosted in the cloud, encompassing applications, data, and infrastructure. It’s important to note that the responsibility for cloud security is typically shared between organizations and their cloud service providers. In this shared responsibility model, cloud service providers assume the responsibility for securing the underlying cloud environment, while organizations are accountable for securing the specific resources and data they place in the cloud. This division of responsibilities helps ensure a comprehensive approach to cloud security.
5. Mobile Security
Mobile security pertains to various cybersecurity measures employed to safeguard mobile devices, including smartphones, tablets, and laptops. The objective is to prevent unauthorized access to these devices and to minimize the risk of them being exploited as entry points to gain access to and navigate through networks.
6. Internet of Things (IOT) Security
IOT (Internet of Things) security is focused on mitigating the vulnerabilities introduced by the increasing number of interconnected devices within organizations. It encompasses various cybersecurity strategies to identify and categorize these devices, segment them to restrict their network exposure, and address potential threats linked to unpatched firmware and other related weaknesses. The goal is to enhance the security of IoT ecosystems and protect organizations from potential risks.
7.Endpoint Security
Desktops, laptops, mobile devices, servers, and other endpoints serve as the primary entry points for cyberattacks. Endpoint security plays a crucial role in safeguarding these devices and the data they contain. Additionally, it encompasses a range of cybersecurity measures aimed at protecting networks from cyberattacks that exploit these endpoints as entry points. The goal is to fortify both the devices themselves and the broader network infrastructure.
8. Supply Chain Security
Supply Chain Security encompasses measures to verify the authenticity of components, detect vulnerabilities, and establish trust within the supply chain. It also involves monitoring and managing third-party risks, as well as establishing secure practices and standards for supply chain partners to minimize the potential for cyber threats and breaches that could compromise the integrity and confidentiality of the supply chain and the organization it serves.
What are the most prevalent cybersecurity threats that can damage a business?
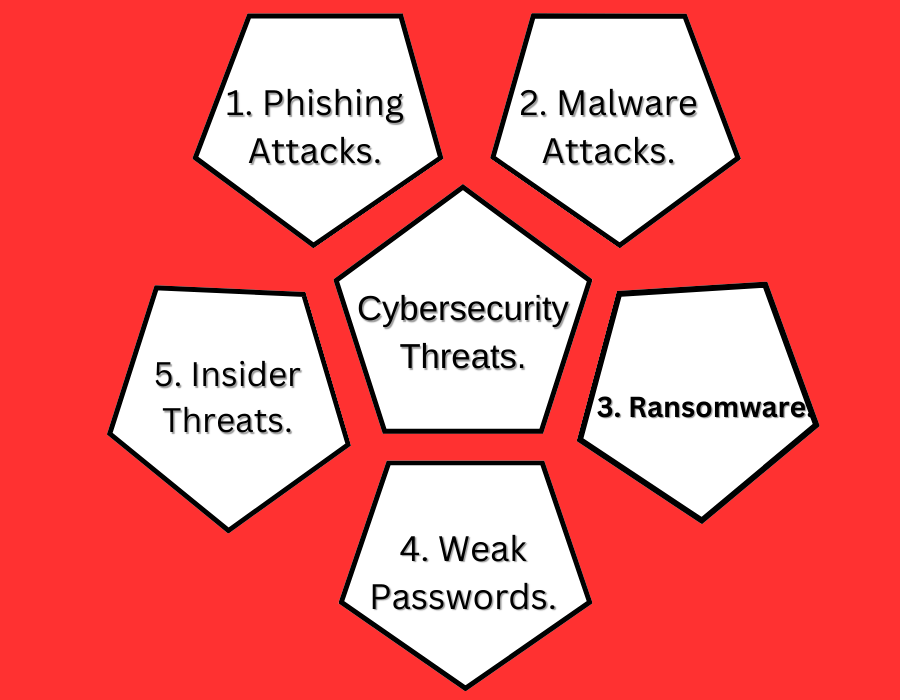
Phishing attacks represent a significant and pervasive threat to small businesses, accounting for a staggering 90% of all breaches. These malicious campaigns have seen a troubling 65% increase over the past year and have inflicted over $12 billion in losses. In phishing attacks, perpetrators impersonate trusted contacts to lure unsuspecting users into clicking on malicious links, downloading harmful files, or disclosing sensitive information, account credentials, or access. The complexity of phishing attacks has evolved, with attackers becoming adept at convincingly mimicking legitimate business contacts. Business Email Compromise has also emerged, where cybercriminals employ phishing campaigns to pilfer high-level executive email account passwords, subsequently using these accounts to fraudulently request payments from employees. One of the challenges in combating phishing attacks is their reliance on social engineering to exploit human vulnerabilities rather than technical weaknesses. However, there are technological defenses to counter them. Robust Email Security Gateways like Proofpoint Essentials, Mimecast, and cloud-based email security providers like IRONSCALES can prevent phishing emails from infiltrating employees’ inboxes. These solutions empower users to report phishing emails, allowing admins to remove them from all inboxes. Multi-factor authentication (MFA) plays a crucial role in mitigating phishing risks. MFA adds an extra layer of security during the authentication process, typically involving SMS codes, trusted device notifications, or biometric checks. With MFA, even if attackers compromise usernames and passwords through phishing, they would still be unable to access an account without the unique piece of information known only to the user. The final layer of defense against phishing attacks is Security Awareness Training. These solutions enable businesses to safeguard their employees by testing and training them to recognize and report phishing attempts, enhancing overall security awareness.
2. Malware Attacks.
Malware stands as the second significant threat confronting small businesses, encompassing a wide range of cyber dangers such as trojans and viruses. This umbrella term refers to malicious code crafted by hackers with the intent of infiltrating networks, pilfering data, or causing destruction to computers. Malware typically finds its way into systems through malicious website downloads, spam emails, or by connecting to other infected machines or devices. The impact of these attacks can be especially devastating for small businesses, often resulting in device malfunctions that necessitate expensive repairs or replacements. Additionally, malware can serve as a backdoor for attackers to access critical data, putting both customers and employees at risk. Small businesses are more prone to employ individuals who use personal devices for work, which can streamline operations but also heighten susceptibility to malware attacks due to the greater risk associated with personal device usage. Businesses can shield themselves from malware threats by implementing robust technological defenses. Endpoint Protection solutions play a crucial role in safeguarding devices against malware downloads and provide administrators with centralized control for device management, ensuring that all users’ security remains up to date. Web Security is equally important, preventing users from accessing malicious websites and downloading harmful software.
3. Ransomware.
Ransomware is one of the most common cyber-attacks, affecting thousands of businesses each year. These attacks have become more frequent because they can be quite profitable. Ransomware involves encrypting a company’s data, making it inaccessible, and then demanding a ransom payment to unlock the data. This leaves businesses facing a difficult choice – pay the ransom and risk significant financial loss, or risk service disruptions and data loss. Small businesses are especially vulnerable to these attacks. Reports indicate that 71% of ransomware attacks target small businesses, with an average ransom demand of $116,000. Attackers know that smaller businesses are more likely to pay a ransom, as their data is often not backed up, and they need to get back up and running quickly. The healthcare sector is particularly susceptible to these attacks, as locking patient medical records and appointment schedules can have a devastating impact, potentially leading to closure unless a ransom is paid. To prevent these attacks, businesses need strong Endpoint Protection on all their devices. These solutions help stop ransomware attacks from effectively encrypting data. Endpoint protection solution Sentinel One, for instance, provides a ‘ransomware rollback’ feature, allowing organizations to rapidly detect and counter ransomware attacks. Additionally, businesses should consider implementing an effective cloud backup solution. These solutions securely backup company data in the cloud, reducing the risk of data loss. Various data backup methods are available, so it’s crucial to research and choose the one that suits your organization’s needs.
4. Weak Passwords.
Another significant threat facing small businesses is the use of weak or easily guessable passwords by employees. Many small businesses rely on multiple cloud-based services that require distinct accounts, which may contain sensitive data and financial information. When employees use weak passwords or reuse the same passwords for multiple accounts, it can jeopardize the security of this data. Small businesses are particularly susceptible to compromises resulting from employees using weak passwords, often due to a lack of awareness regarding the potential consequences. On average, 19% of enterprise professionals employ easily guessable passwords or share passwords across multiple accounts. To ensure that employees use strong passwords, businesses should consider implementing Business Password Management technologies. These platforms assist employees in managing passwords for all their accounts, offering suggestions for robust passwords that are difficult to crack. Additionally, businesses should explore the adoption of Multi-Factor Authentication (MFA) technologies. As previously mentioned, MFA solutions require users to provide more than just a password to access business accounts. This may involve multiple verification steps, such as a passcode sent to a mobile device. These security measures are effective in preventing unauthorized access to business accounts, even if an attacker manages to correctly guess a weak password.
5. Insider Threats.
The insider threat represents a significant concern for small businesses. It refers to the risk posed to an organization by the actions of its employees, former employees, business contractors, or associates. These individuals have access to critical company data and can potentially cause harm through motives like greed, malice, or simply due to ignorance and carelessness. According to Verizon, 25% of data breaches result from insider threats. This problem is on the rise and can jeopardize both employees and customers while inflicting financial damage on the company. Within small businesses, insider threats are becoming more prevalent as more employees have access to multiple accounts containing substantial data. Research has indicated that 62% of employees admit to having access to accounts they probably don’t need. To mitigate insider threats, small businesses must foster a strong culture of security awareness within their organization. This proactive approach helps prevent insider threats stemming from ignorance and enables employees to detect early signs of a data breach or an attempt to compromise company data.
Cyber Security jobs
The field of cybersecurity is experiencing rapid growth, creating a demand for skilled professionals across entry, mid, and advanced-level positions. Projections indicate that the demand for cybersecurity jobs will increase by 18% in the next five years. Cybersecurity professionals play a crucial role in safeguarding computer networks and data from unauthorized access, misuse, or potential destruction. Within this field, there are various roles with differing skill requirements. Entry-level positions typically necessitate a high school diploma or GED equivalent, coupled with some on-the-job training. Mid-level positions call for an associate’s degree in computer science or a related field, at least one year of practical experience, and specialized educational coursework. For advanced-level positions, a bachelor’s degree in computer science or a related field is typically required, along with a minimum of three years of professional experience and additional specialized education.
How cybersecurity works?
Cybersecurity refers to the practice of protecting digital systems, like networks and software, from online threats. These threats often aim to gain unauthorized access, alter, or harm sensitive data, demand money from users, or disrupt everyday business operations. Cybersecurity primarily works through preventive measures, like software updates and firewalls, that help detect and block malicious activity. In this blog, we’ll define cybersecurity, explain how it functions, and explore its different types
Cybersecurity Education and Specialization.
How Cyber Security Benefits AbhinavDCS?
At AbhinavDCS, we specialize in implementing SSL solutions that enhance the security of your online activities. SSL, which stands for Secure Sockets Layer, creates a safe connection between your web browser and the websites you access. This encryption guarantees that your private data, such as passwords and payment information, stays confidential and shielded from potential online risks. With our SSL expertise, you can have confidence that your internet interactions are protected, giving you peace of mind in today’s digital landscape. Our services prioritize encryption, verification, data integrity, and the use of HTTPS to ensure your online security.
To know how to create an SSL Certificate do visit our previous blog:
HOW TO CREATE SSL CERTIFICATE WITH CERTBOT